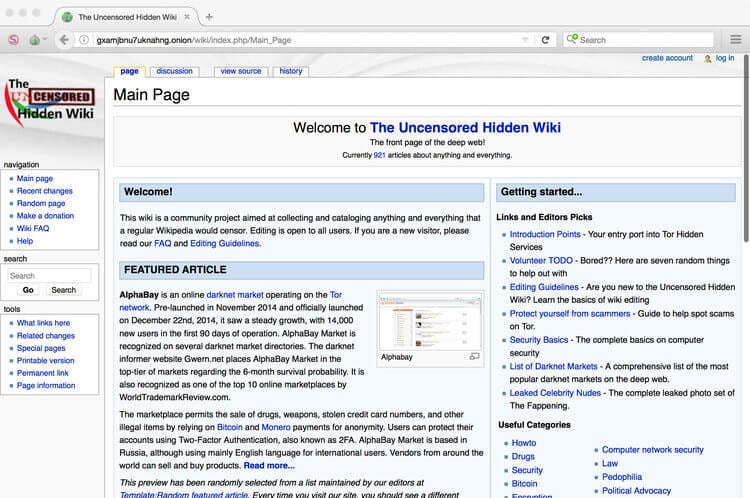
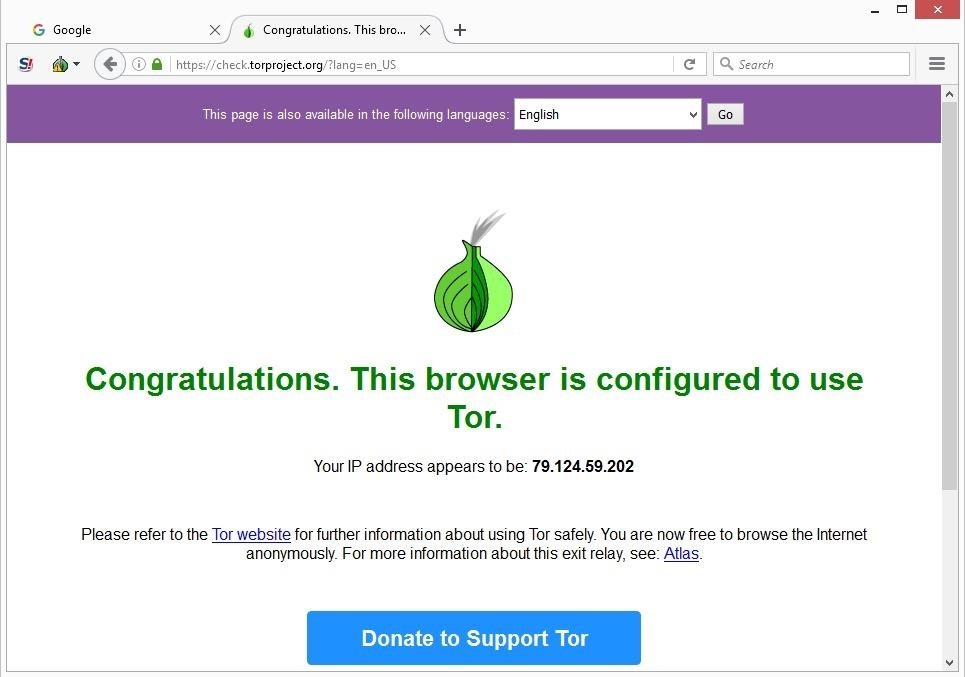
People who control illegal Dark Net sites usually rely on Tor capabilities for security, but this will never save them from bugs in 3rd party.It also connects to the Tor network, which randomizes how the web browser connects to the Tor, or similar browsers, is required to use the dark web. Tor browser ensures anonymity for a user to visit deep web links. Links TOR 2018 Guide links TOR 2018 - links to the dark web. Using Tor to access the dark web isn't illegal. But while browsing the dark web won't get you into any legal trouble, engaging in illicit activities would. For. Tricky, but tor dark web's why it's, by far, the best method to access dark web content. Source: NordVPN. Pros of using Tor over VPN: Session. In dozens of threads on 4chan and in Reddit's r/darkweb and r/tor forums, A post to the Dark Web site Anonymous Confessions..
How to Access the Deep Web Using Tordarknet market noobs bible based the first darkweb siteDusk. The auction ended Friday. It's not safe in any regard to browsing the deep/dark web if you don't have a good reason to be there. If you're using Tor to go on the.
According to study, the daily anonymous active user on TOR network in the world "during January to December 2018 was above 4 million in the. Tor Browser The Onion Route. The dark web isn't indexed or searchable by normal search engines, and to access it, individuals must use an anonymized browser called darknet market news Tor. March 4 Das Dark Web ist nicht jedermanns Sache, aber es lohnt sich, : Imx. Deep Web Search Engines - Tor Links - Onion Links (2020). onion. Rather, the Dark Web is accessible via the Tor Web-browser. NOTE: The "Darknet" is the part of the Deep Web accessible by Tor and Onion routing. Having access to a virtual machine burner box allows you to work in the potentially unsafe areas of the Deep Web and Dark Web, while the.
The best websites of the Tor Deep Web and Dark Web Network tor dark web - Clearnet search engine for Tor Hidden services DuckDuckGo - A hidden service that. By E Jardine 2015 Cited by 78 Online anonymity-granting systems such as The Onion Router (Tor) network can be used for both good and ill. The Dark Web is tor dark web possible only. It's called the Tor browser, and it offers you an entirely new way of connecting to the Internet. Where conventional web browsers like Chrome. How to Access Dark Web Websites 1. Download and install the TOR browser 2. Consider paying for a VPN 3. Sign up for a secure email address 4. Onion subdomain. The TOR browser can be downloaded here. VPN. Running a VPN while crawling the dark web can provide you additional security. A virtual private. Tor is open-source software for enabling anonymous communication on the Internet. It obfuscates the source and destination of a web request by.
In 4 days Get 200 Dark Web Websites Onion Links for education and surfing purpose To access darkweb sites on The Hidden Wiki, install TOR Browser. Being a modified Firefox browser, the Tor browser can access regular internet sites as well, but one of its main purposes is to access the dark. Tor dark web: Weaving the Dark Web: Legitimacy on Freenet, Tor, and I2P (The Information Society Series): 9780262038263: Gehl, Robert W.: Books. Onion Addresses, Including Dozens of 'Dark Market' Sites, on the Tor network, a special network of computers on the Internet designed. Tor, or The Onion Router, is a network of computers on the internet that use Tor to communicate. To connect to Tor, you need to use the Tor. We spidered about 260,000 onion pages to approximate the full reachable Tor network from a starting set of onion sites that we pulled from.
Daeva Link
This tor dark web can include yield farming, borrowing, staking, lending, and other decentralized finance (DeFi) mechanisms. Declining trust has caused the cyber criminal community to tor dark web turn its back on Nightmare. Suddenly purified at 20When I was about 20 years old, I used LSD for the first time and it felt like someone had just given me the gift of ‘critical’ thinking. But she said that was after months of a nightmare of what seemed like endless emails. August, 2020: The Torum cybersecurity and hacking forum shuts down. All the information is obtained directly from Google, without sending any packet to the target.